Achieving Cloud Compliance with AWS

Do you think compliance matters?
As Software Engineers we build products belong to various domains. Regardless of the domain, the responsibility of securing our customers’ sensitive data rests on our shoulders. You could be running your product on-premises, You could be running it on cloud or may be you are planning to migrate to cloud. Whichever the case, ‘customer data security’ is important.
Oftentimes, you must adhere to inherent regulatory compliances of specific product domains as well. For example if you are into the domain of e-commerce and handle credit card information of the users, you must be PCI DSS compliant. If you are into the healthcare domain, you probably have to be HIPAA compliant. Likewise, there are many regulatory compliances exist in various domains.
If your product belongs to such a domain you must adhere to related compliances. Failure to compliance could lead to legal actions and major penalties.
AWS to the Rescue :)
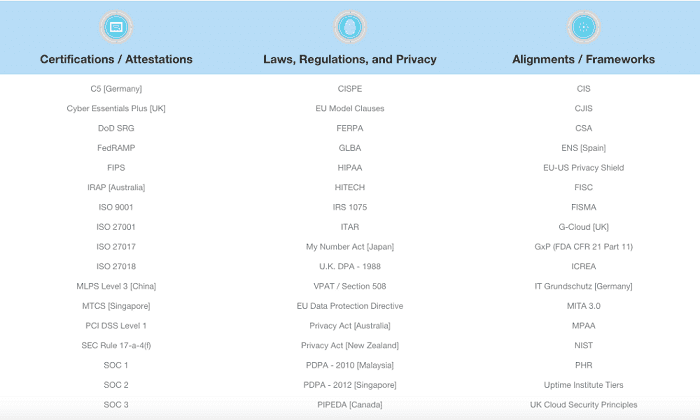
If your systems happen to be in the AWS cloud platform, you are lucky. AWS offers many services to achieve compliance much easier. Have a look at the Key AWS Certifications and Assurance Programs in the below figure.
The rest of this post will focus on how AWS supports to achieve PCI DSS(The Payment Card Industry Data Security Standard) compliance for an e-commerce company. We will discuss about the usage of different AWS services in achieving it.
PCI DSS Compliance
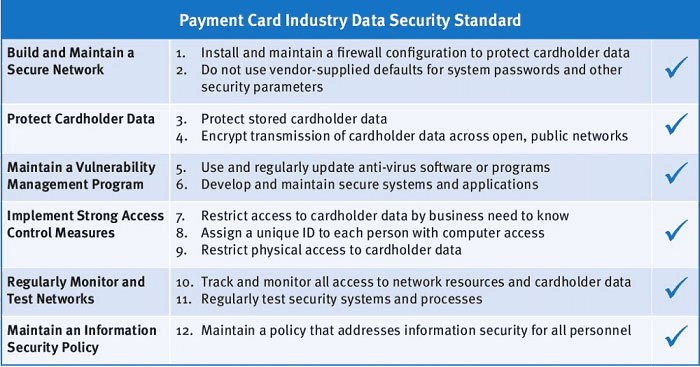
PCI DSS compliance must be implemented by all the entities involving in processing, storing or transmitting credit/debit cardholder data. If your product accepts VISA, MasterCard, American Express and etc… credit/debit cards from customers to process payments, you must adhere to PCI DSS compliance. Have a look at the PCI DSS reference guide. There are 12 major requirements to achieve the PCI Data Security Standards. Under each of the major requirement, there are a lot of sub-requirements to satisfy by the customer. Download the PCI DSS standard published by PCI Security Standards Council.
Install and maintain a firewall configuration to protect cardholder data
The first requirement enforces to have firewall at each internet connection. Sounds difficult to implement? Well it’s not.
***AWS Services***: We can make use of VPC, Security Groups, NACALs and Config when architecting our product. Here is one way you can do it.
- Use VPCs to split your network into public and private subnets
- Cardholder data goes into the private subnets (Not publicly accessible)
- Limit access based on need-to-know (Don’t give access to everyone)
- Use Ingress and Egress VPC Security Group Policies for individual resources and VPC NACLs in subnet level
- Deploy a formal change management process (Always know what changed and when)
Do not use vendor-supplied defaults
Sometimes we do this. We keep the defaults passwords/configurations provided along with the software at installation. This shouldn’t be done as those configurations may not be optimal for your needs.
***AWS*Services**: Use of Amazon supplied AMIs — They don’t contain default configurations.
- Remove and disable unnecessary software and applications. Firstly, try not to use unnecessary software at all
- Customize your software configurations to suite your environment
- Do not run your web-server and the DBMS on one instance. Well, this is a common fact in terms of scalability and security
- Use SSH private keys with additional Multi Factor Authentication (MFA)
Protect stored cardholder data
This is about encrypting data at rest(data that is stored) to protect card holder data.
***AWS*Services**: Leverage AWS services that supports encryption. Such as EBS(Elastic Block Storage), S3 Encryption, KMS (Key Management Service), RDS(Relational Database Service)
- Encrypt your EBS volumes attached to EC2 instances
- Leverage Server Side bucket encryption with S3
- Enable encryption on your RDS
- Can use commercial or open-source encryption tools
- Only store minimal cardholder data
- Rotate encryption keys regularly
Encrypt transmission of cardholder data across open, public network
This is about encrypting data in transit(data that travels among hops).
***AWS*Services**: ELB, Network ACLs, Security Groups, Customer Gateways, Virtual Private Gateways, VPN Connections, AWS Direct Connect
- Encrypt data using SSL with a secure cipher suite
- Terminate SSL at the ELB or at the Web server
- Setup VPN or Direct Connect in communication with AWS and your on premises
Use and regularly update anti-virus software or programs
In terms of vulnerability management, AWS does not provide anti-malware for customer EC2 instances. AWS customers have to,
- Apply Antivirus software at EC2 instances and ensure they auto-update
- Use vulnerability preparing for audits
Develop and maintain secure systems and applications
***AWS*Services**: AMI, CloudTrail, CloudWatch, Config, CloudFormation, CodeCommit, CodeDeploy, CodePipeline
- Review, test and apply security patches regularly
- Develop software according to PCI AppSpec/OWASP guidelines
- Use IAM and remove any test IAM users from non-test environments
- Ensure MFA and IAM Policy are being used
- Enable CloudTrail, ELB and S3 logging and collect logs for audit trails
- Any changes to environment are to be documented and approved
- Avoid manual deployment. Use CloudFormation, CodeDeploy, Chef and Puppet
Restrict access to cardholder data by business need-to-know
***AWS*Services**: IAM, Directory Services
- Use number of IAM users and restrict policies to specific capabilities based on business need
- Optionally can use SAML and SSO for AWS management console users
Assign an unique ID to each person with computer access
***AWS*Services**: IAM
- Do not use root AWS account at all if possible
- Ensure users are using IAM accounts or SAML/SSO
- Enable Multi Factor Authentication for all AWS accounts
- Do not use shared credentials anywhere
Restrict physical access to cardholder data
You don’t have to worry about this at all. According to the shared responsibility model, AWS manages and maintains their physical infrastructure and security. AWS covers this for you.
Track and monitor all access to network resources and cardholder data
***AWS*Services**: CloudTrail, CloudWatch, S3
- Regularly review CloudTrails logs to identify critical activities
- Enable S3 Logs, VPC FlowLogs for better log management.
- Use HIDS/HIPS centralized logging to monitor login activities, file integrity changes and security events
Regularly test security systems and processes
Amazon’s Attestation of Compliance(AOC). AWS tests their systems annually for security vulnerabilities. Similarly you have to test your system annually as well.
- Vulnerability Scanning
- Penetration Testing
- Inform AWS before penetration testing
- Have a third party audit environment
Maintain a policy that addresses information security for all personnel
- Security policies should be documented and shared with all the personnel
- AWS inventory and account information should be updated regularly
- Have and incident response plan ready before a breach
- Put 24/7 monitoring in place to enable rapid response
So far we have discussed about how to achieve PCI DSS compliance with AWS Cloud. AWS itself is compliant to many cloud compliances including PCI DSS, but to claim your product’s compliance you have to use necessary services provided by AWS.
For more from Manoj, check out his blog over on Medium